What Is Data Compliance?
Data compliance is the practice of storing and managing sensitive data in a way that keeps it safe from theft, loss, corruption, and misuse. With data such a precious commodity for most organizations, protecting customers’ personally identifiable information (PII) and financial details has become a key operational priority.
Across different sectors and geographies, regulators have put in place rules that ensure this happens. Organizations must follow regulations that address how their data is captured, organized, accessed, and managed. Failure to comply can result in substantial fines.
Key Data Compliance Regulations
There is more data compliance now than there has ever been. Depending on the industry an organization operates in, there can be many different regulators to appease, some focused on that industry and others that look at data compliance more generally.
Financial Services (FS) is a sector that has a lot of data compliance regulations. The Payment Card Industry Data Security Standard (PCI-DSS) stipulates requirements for processing, storing, and transferring payment card data. The Markets in Financial Instruments Directive II (MiFID II) aims for more harmonized regulation across European Union (EU) financial markets and seeks to establish greater transparency for participants.
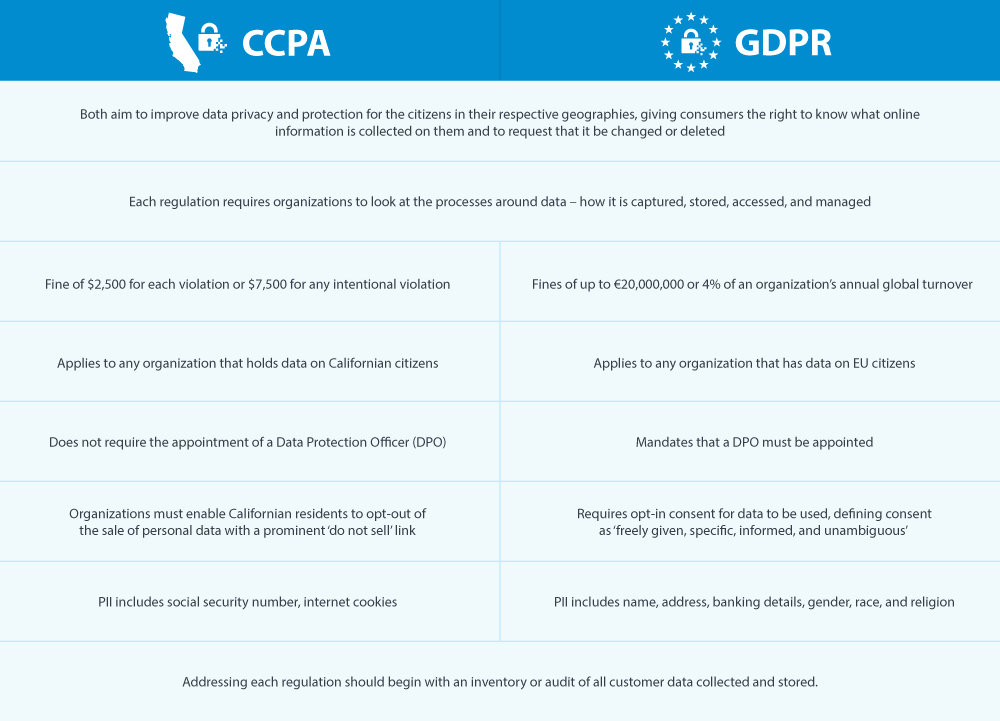
These are just two examples of FS data compliance. There are many others and plenty more focused on other industries. There is also more general data compliance, such as the EU General Data Protection Regulation (GDPR) and California Consumer Privacy Act (CCPA). Both seek to give consumers more control over their personal information and more power over how organizations collect and manage that data.
What Is GDPR and Who Does It Affect?
GDPR is probably the best-known data compliance regulation after it was introduced following years of discussion in 2018. The most significant change to data privacy laws in a generation, GDPR means that organizations must now store and manage the consumer data they hold in a certain way.
GDPR applies to organizations in every sector and country in the world – if an organization holds any data on EU citizens, it must comply with GDPR, irrespective of its location. Failure to comply will result in fines of up to €20,000,000 or 4% of an organization’s annual global turnover, whichever is greater.
The biggest GDPR fine (to date) was for Amazon in 2021. The online retailer revealed in its financial records that regulators in Luxembourg are fining the retailer €746 million (£636m) for breaching GDPR. After three years of GDPR, there have been around 880 fines issued to date, for a combined total of approximately €1,29 billion.
What Are the Main GDPR Compliance Challenges?
When transformative data compliance legislation such as GDPR is introduced, it brings a number of challenges of which organizations must be mindful.
First and foremost is that GDPR can be a highly complex undertaking. Any organization embarking on GDPR data compliance must first conduct an audit of its systems, looking at what data must be collected, where it is stored, how it is used, who has access to it, for how long, and for what purpose?
The larger the company, the more complex this becomes.
GDPR means that customers have much more control over the data that organizations hold on them. Data cannot be obtained without a customer's consent, and people can ask questions about how their data is used. This includes questions such as the reason for having this data, who will be handling it, and how long it will be stored? Organizations must also manage requests for correction or removal of data.
Organizations must also spend time, resources, and budget on establishing processes and implementing GDPR technologies. GDPR data compliance is an opportunity for organizations to get their data organized, compliant, and protected, but it is not without challenges.
GDPR Compliance Checklist
For any organization that wants to be compliant with GDPR – and that should be all of them – this GDPR compliance checklist is a sensible place to begin.
Establish a culture of data compliance
The requirements for GDPR are such that it requires a collective effort to stay onside. This should include regular training with staff on best practices for data handling generally, GDPR requirements specifically, and cybersecurity.
Get the board to buy in
The penalty for non-compliance with GDPR should ensure that the c-suite takes requirements seriously. If the board is not focused on GDPR, it's likely the rest of the organization won't be either. A top-down approach is essential for GDPR data compliance.
Stay on top of data breaches
Accidental errors in email are the primary cause of data breaches. Human error is hard to mitigate, so an effective email security solution to detect and remove unauthorized sensitive data from emails and automatically encrypt any authorized data will provide an additional layer of protection.
Understand your data ecosystem
It’s hard to achieve data compliance when you do not know what data you have or where it is stored. Understanding your organizational data ecosystem is a crucial GDPR challenge. It must include data classification on where data enters and exits the organization and where it is stored.
Be mindful of remote workers
Many organizations now operate using a distributed or hybrid working model, meaning employees are sending sensitive data to and from their homes. A Managed File Transfer (MFT) system can help meet GDPR requirements, securing personal data through encryption, performing integrity checks on successful file transfers, and providing audit trails and reporting for every transfer.
Getting GDPR buy-in from the board can be a challenge.
Read our report, The GDPR Divide: Board views vs Middle Management, to learn more about bridging the GDPR governance gap.
CCPA Compliance
The CCPA is data compliance legislation that addresses consumer data privacy in the state of California in the US. It was the US's first-ever state data privacy law and came into effect on 1 January 2020. Just as GDPR affects any organization with data on EU citizens, CCPA will affect any organization that does business in California or holds data on customers residing in California.
Non-compliance with CCPA can result in significant fines. The state of California can charge an offender directly — civil penalties of $2,500 for each violation or a $7,500 fine for any intentional violation not addressed within 30 days. California consumers can also bring a civil lawsuit against organizations that do not abide by the CCPA.
CCPA changes the definition of what type of data organizations must manage and account for. This includes IP addresses, geolocation data, biometric data, and other unique identifiers such as cookies and device IDs. CCPA is game-changing legislation, as impactful to the state of California as GDPR is to the EU.
CCPA vs. GDPR
CCPA and GDPR are the two most high-profile pieces of data compliance legislation. While there are similarities between the two, they are also several notable differences.
What Is PCI Compliance?
PCI compliance refers to the Payment Card Industry Data Security Standard (PCI DSS). This establishes a series of requirements that ensure the secure processing, storing, or transmitting of payment card data and protects organizations and their customers against credit card fraud.
There are 12 main requirements for PCI compliance, including the use and maintenance of firewalls to prevent unauthorized access, the use of proper and effective password protection, and encryption of all credit card data. The main concerns are around unstructured data, with credit card data appearing in emails and documents transferred around the company creating additional risk.
PCI compliance involves many standards and can be a complex undertaking. But doing so ensures that systems are secure, and customers can trust you with sensitive card payment information, increasing retention and loyalty. It also involves organizations committing to PCI DSS as an ongoing process. This helps prevent security breaches and data theft and can help tighten processes around their data compliance requirements.
PCI Compliance and Data Loss Prevention
PCI compliance and Data Loss Prevention (DLP) are hugely complementary to each other. Sending and receiving emails with credit card details is very common. If someone replies to such an email, the organization sends PCI data over an open channel, which is a data breach.
Traditional DLP solutions identify the card number and block the email known as 'stop and block.' It's also cumbersome and ineffective. People do not know if emails have been received, and IT or compliance departments need to get involved to remedy the problem.
Adaptive Data Loss Prevention (DLP) is a far more effective solution. It relies on:
Clearswift’s Deep Content Inspection Engine is at the heart of adaptive DLP. It strips back all inbound messages and will only detect and remove information that breaks PCI DSS guidelines.
MFT solutions also play a pivotal role in PCI compliance. The GoAnywhere MFT comes with comprehensive security controls and detailed audit trails, making it a natural process to comply with PCI DSS and other data compliance.
Achieving PCI compliance is an ongoing challenge for any organization that deals with credit card payments and data.
To learn tips and tricks to ensure your organization is PCI compliant, download this PCI Compliance Best Practices Guide.
The Health Insurance Portability and Accountability Act (HIPAA)
The Health Insurance Portability and Accountability Act (HIPAA) came into force in the US in 1996 to reduce health care fraud and abuse. It involved the creation of national standards to protect sensitive patient health data from being shared and disclosed without consent or knowledge.
There are two principal standards for HIPAA - the Privacy Rule and Security Rule. The Privacy Rule establishes national standards for protecting health information, specifically PII, Protected Health Information (PHI), and electronic Protected Health Information (ePHI).
The Security Rule operationalizes Privacy Rule protections by addressing the administrative, physical, and technical safeguards that healthcare organizations must put in place to secure and protect electronically stored and shared ePHI. These protections help ensure the protected health information’s confidentiality, integrity, and security.
With health data increasingly stored, shared, and managed online, but with patient privacy still a major concern, HIPAA has grown in importance over the years. Failure to comply with HIPAA can land an organization with a substantial fine, while criminal charges and civil action lawsuits are possible a breach.
How to Ensure HIPAA Compliance
Ensuring HIPAA compliance is essential for any US organization that holds healthcare data. As with other forms of data compliance, establishing an environment conducive to data compliance is the best place to start. This should include:
Related Resources
See for yourself how our range of data compliance solutions can help your organization stay on the right side of regulatory requirements.
Schedule a demo on the product of your choice.