In today’s global information age, there is a need to protect information. Not all information is created equal, so rather than trying to protect everything, critical information needs to be singled out. In order to protect the information, there is a need to be able to track it and then to apply the appropriate protection.
The Information Governance Server (IGS) sits in the heart of the network and provides a central repository for critical information. The information is not just full files, but also partial file information. Information is registered and then tracked by the system through fingerprinting. The IGS database contains the full fingerprint values as well as the partial information fingerprints. The fingerprints are created using a one-way hashing algorithm to ensure that any data on disk cannot be reverse engineered into its original format.
IGS with its ability to track millions of pieces of information can then enhance Data Loss Prevention solutions by enabling the detection of free form information that has been registered.
Data Loss Prevention is a key requirement for business integrity and data security. Data leaks can not only lose critical information, but it can also cause major corporate embarrassment, incur high remediation charges and can also incur heavy fines from regulatory bodies.
Organizations have to ensure that any monitoring of information flow is consistently enforced for it to be effective. IGS can monitor information as it crosses the organizational boundary as well as internally, providing the ‘track and trace’ functionality which is needed as part of an Information Governance or Critical Information Protection strategy.
IGS is designed for ease of use by all those within the organization as well as the demanding situations that today’s Compliance Officers frequently find themselves in.
Simple Information Classification
Document owners can access the system using their existing Windows credentials to securely register data with the IG Server. In the easy to use process, the user can:
- Manage the classification of the data from a customer defined list (Top Secret, Secret, Informational, Unclassified, etc.)
- Register content into logical groupings of the data, for example if the system is being used by the Human Resources group, then registered data may be grouped in the “Payroll” collection
- Add text to be “whitelisted” into the system to prevent false positives
- View dashboard feedback of the number and types of violations of their registered data
Adhering to Policies and Remaining Compliant
Compliance Officers are given access to oversee who and what is being registered. Whilst they can’t read the content they can observe which departments and users are registering data and how many times it is being detected in traffic flow using the built in reports.
Definition and Management of Content
Compliance Officers are also responsible for the definition and management of content for a corporate whitelist.
Multiple reports are available to the Compliance Officer to demonstrate the volume of registrations, incidents and user behavior.
Every data interception point can provide transaction information back to the IG server. This data permits the Compliance officer to “track and trace” the data around and across an organization as it passes from user to user and through different systems.
The Clearswift Information Governance Server will:
- Enable tracking of information at both the file and sub-file information level
- Enhance DLP solutions by blocking registered content when it is attempted to be communicated to unauthorized recipients
- Enable tracing of information in ‘after-the-fact’ analysis of communication flows
- Enable the creation of information provenance and user interaction reports
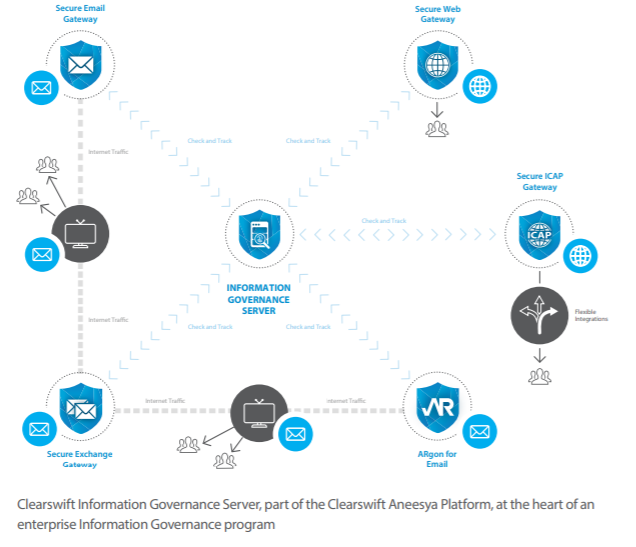
The Clearswift Information Governance Server is designed to be deployed in conjunction with the Clearswift Secure Gateway products and augment their DLP and Adaptive Redaction functionality, plus future offerings from Clearswift and our technology partners as part of our critical information protection strategy.
- Clearswift Secure Email Gateway: Track, trace, and control information contained in email across the organization boundary
- Clearswift Secure Exchange Gateway: Track, trace, and control information as it travels in internal email
- Clearswift Secure ICAP Gateway: Track, trace, and control information which passes through an ICAP compliant web gateway
- Clearswift Secure Web Gateway: Track, trace, and control information as it travels to and from the Internet
Work securely and productively with Clearswift
See what the Clearswift Information Governance Server can do for your organization.