Securing Information at the Endpoint
Be confident your enterprise security and compliance policies extend to your endpoints distributed inside your organization or at remote locations. Clearswift's Endpoint DLP solution automatically discovers critical data that requires the security demanded by industry regulations, protects against unauthorized information copy or transfer, and controls device connectivity to prevent malicious attacks, and malicious or accidental data loss.
Solution Features
Unparalleled Endpoint Information Inspection, Detection and Security
Utilizing the Clearswift Deep Content Inspection Engine, the Clearswift Endpoint DLP Agent discovers critical information wherever it is stored (at rest) on desktops, notebooks, servers, network and cloud shares. Transfer of critical information (in use) can be logged, blocked or encrypted and the solution provides automated policy-based remediation. Granular organizational policy provides the necessary flexibility to permit multiple behaviours, depending on the user and destination of file operations.

Data-at-Rest vs. Data-in-Use
Automated Data Discovery and Security of Data-at-Rest (DAR)
Detect and secure critical information based on content or regulation, including cloud and file server storage. Mitigate unsecured critical information risk based on policy, including moving the files to a more secure location within a network, leaving breadcrumbs behind for users to be made aware of where critical information has been moved to. Built-in and customizable lexical expressions enable the discovery of a variety of critical information types including PII, PCI and other sensitive data.
Context Aware Data-in-Use (DIU) Policies
Flexible policies and context-aware content inspection mean that you no longer have to choose between the productive use of removal media and unacceptable risk. A policy which is too restrictive means that people either cannot work effectively, or they will find way to bypass company security policy. Rules can be created that can, for example, block all spreadsheets containing particular keyword terms from being copied to external devices, or automatically encrypt files when transferred, meaning the contents cannot be read if a device was to be left behind on a train, taxi or other public place.
Granular Device Control
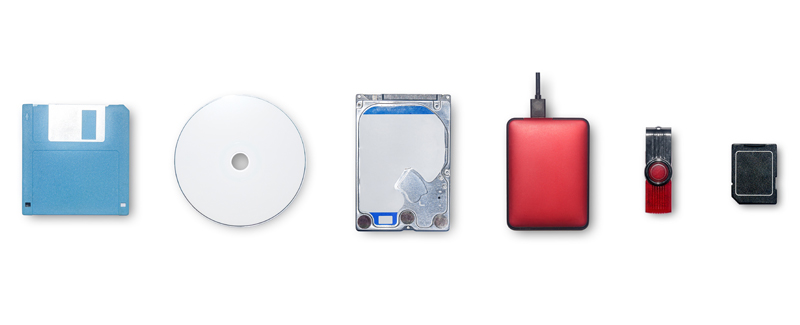
The Clearswift Endpoint DLP Agent also provides a fine level of granular control over removable media devices, including USB sticks, CDs, DVDs and variety of other modern device types. Granularity can restrict use to specific device manufacturers or to individual devices to ensure only authorized devices are used.
Related Resources
Security that Doesn't End
Unprecedented layer of real-time monitoring, inspection and sanitization bolts onto an organization existing security infrastructure to extend beyond its perimeter and provide the agile defense upgrade needed to future-proof protection from unknown threats.
